What are the Security Risks of Using Traditional Keycard Systems?
Traditional access methods, including physical keys and keycards, present inherent security risks despite their widespread use. These tangible credentials are susceptible to a range of vulnerabilities that can compromise an organization’s security framework.
- Loss and Misplacement: Keys and keycards are prone to loss and misplacement, creating immediate security gaps. A lost card can grant unauthorized access until it is reported and deactivated, exposing the organization to risk. This human element introduces significant vulnerabilities into the security ecosystem.
- Theft: A stolen keycard poses a direct security threat. It provides an unauthorized individual with immediate entry to restricted areas, often before the credential holder is aware of the compromise.
- Unauthorized Sharing and Duplication: Keycards can be shared or intentionally duplicated, enabling unauthorized individuals to bypass security protocols. This practice erodes individual accountability and complicates the process of tracking access, increasing the risk of internal security threats.
- Compromised PINs: In systems that augment keycards with PINs, the PIN itself remains a vulnerability. It can be observed (“shoulder-surfed”) or guessed, diminishing the intended security enhancement.
These vulnerabilities demonstrate why traditional methods are increasingly insufficient for the demands of modern, high-security environments.

How Does Fingerprint Access Control Improve Modern Building Security?
Biometric access control solutions, specifically those utilizing fingerprint recognition, provide a fundamentally more secure methodology. The strength of this approach is rooted in the unique and inherent nature of biometric data.
- Non-Transferable and Immutable: A fingerprint is an inherent, unique identifier tied to an individual. It cannot be misplaced, forgotten, or transferred, ensuring that the person requesting access is the authenticated user.
- Advanced Forgery Resistance: Unlike keycards, which are simple to duplicate, forging a live fingerprint to bypass a modern system is exceptionally difficult. Advanced biometric platforms do not store raw fingerprint images; instead, they convert scans into encrypted digital templates. Access is granted only when a live scan matches the stored template via sophisticated algorithms.
- Liveness Detection: A critical component of advanced biometric systems is liveness detection. This technology distinguishes between a living finger and a fraudulent spoof attempt, such as a silicone mold or a high-resolution image. By analyzing characteristics like pulse, heat, and skin impedance, these systems make fraudulent access exceedingly difficult.
- Enhanced Audit Trails and Accountability: Every access attempt on a biometric access control system is logged, generating a robust and immutable audit trail. This provides definitive accountability, detailing precisely who attempted entry, at what time, and the outcome. This level of data is invaluable for forensic security analysis.
Global adoption trends reflect these security benefits. The use of biometric access control is projected to grow by 37.5% in 2025, driven by its superior security capabilities compared to conventional methods. For a comprehensive overview of how biometrics are transforming access control, you can read more at Koorsen Fire & Security.
Biometric Access Control vs. Keycards: Which System is More Secure?
To further illustrate the benefits, consider this direct comparison:
| Aspect | Keycards/Keys | Fingerprints/Biometrics |
|---|---|---|
| Loss Risk | High: Prone to misplacement or theft. | None: Cannot be lost or left behind. |
| Theft Impact | Immediate unauthorized access. | Minimal: Requires the user’s physical presence. |
| Forgery | High risk of duplication or sharing. | Near-impossible with integrated liveness detection. |
| Convenience | Requires carrying a physical token. | Effortless, contactless scan. |
| Fraud Reduction | Susceptible to identity compromise. | Proven to significantly reduce identity fraud. |
If You’re Ready to Go Beyond Basic Building Security
If your goal is to secure a single office door, a standalone lock can work well—up to a point. But once you need to manage access for dozens of staff or hundreds of students, track exactly who entered which room, and stop the recurring costs of replacing lost keycards, you’ll get better results with a system that connects everything in one place.
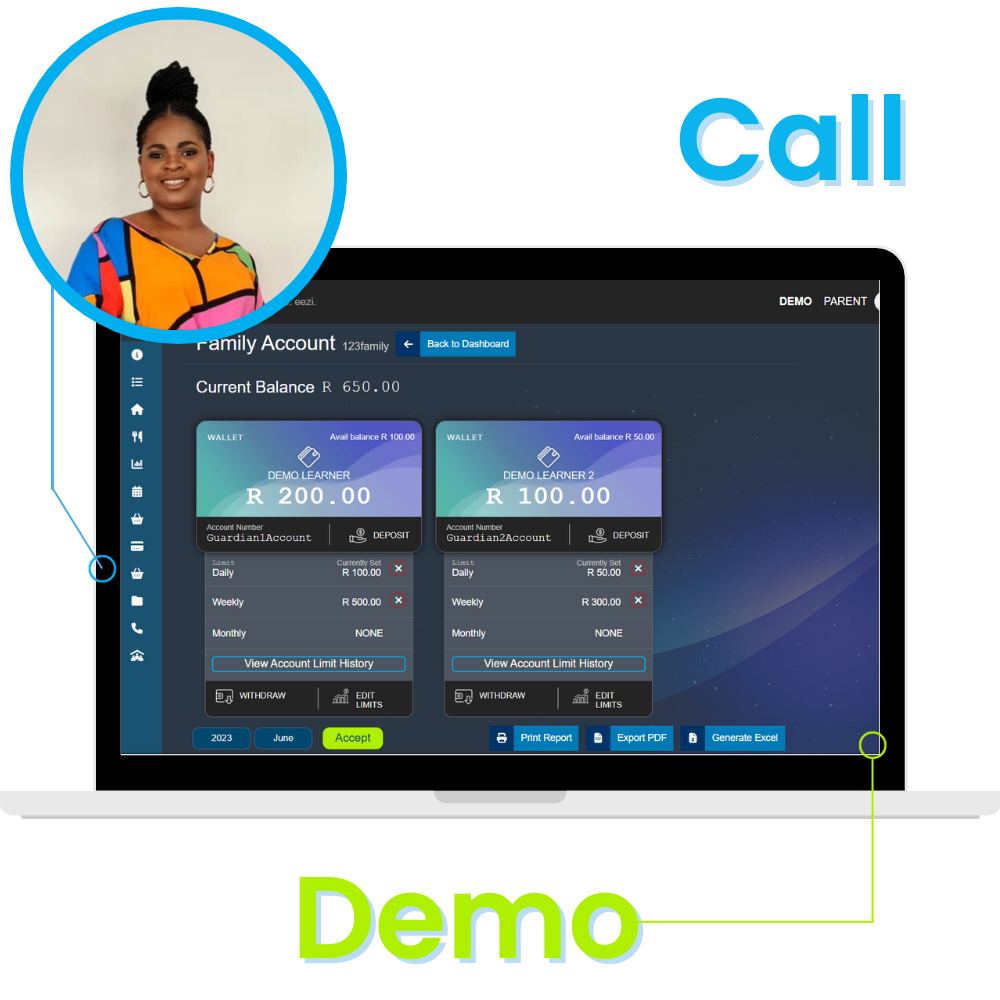
That’s where Eezipay fits. We provide a complete security and management ecosystem designed for South African schools and businesses. By combining high-grade biometric access control hardware with a centralized online portal, we allow you to manage your entire site’s security, attendance, and even internal payments from a single, easy-to-use dashboard.
Next Steps to Secure Your Facility:
-
The Solution: Eezipay Biometric Access Control & Security Systems
How to Reduce Human Error and Identity Fraud with Fingerprint Access Control
A significant percentage of security breaches can be attributed to human error, such as lost credentials or compromised passwords. Biometric systems directly mitigate these human-centric risks by eliminating physical tokens, thereby preventing unauthorized sharing and credential loss. Studies indicate that the implementation of biometric access control significantly reduces identity fraud, making it an essential security measure for high-risk sectors across South Africa. The global biometric industry is forecast to reach over R1.1 trillion by 2027, underscoring its growing adoption as a cornerstone of robust security strategies. To understand how these sensors fit into your broader infrastructure—from the core operational workflow to the specific hardware components—you’ll find a complete breakdown in our Access Control Systems: The Definitive Guide (2026 Update).
Furthermore, while the initial investment in a biometric access control system may be higher than that of a traditional card-based system, the total cost of ownership (TCO) often proves superior. This is due to reduced administrative overhead (e.g., eliminating the need to issue and replace lost cards), a decrease in security incidents, and lower overall operational expenses.
Frequently Asked Questions About Biometric Access Control
1. Is fingerprint access control legal and POPIA compliant in South Africa? Yes. Modern biometric access control systems are fully compliant with the Protection of Personal Information Act (POPIA). Leading systems, like those from Eezipay, do not store actual images of fingerprints. Instead, they store a mathematical, encrypted template that cannot be converted back into a fingerprint image.
2. What happens if there is a power outage or load shedding? Reliable fingerprint access control systems are installed with battery backups or Uninterrupted Power Supplies (UPS). This ensures that your security remains active and doors stay locked or functional even during power interruptions.
3. Is biometric access more expensive than keycard systems? While the upfront cost of biometric hardware is typically higher, the Total Cost of Ownership is lower. You save significantly by eliminating the ongoing costs of buying, printing, and replacing lost or stolen keycards, as well as the administrative time spent managing them.
4. Can fingerprints be “faked” with a photo or a mold? High-end systems utilize Liveness Detection technology. This means the scanner checks for heat, pulse, and skin impedance to ensure the finger is “live” and belongs to a real person, making fraudulent attempts with photos or silicone molds virtually impossible.
Final Summary: Is it Time to Retire Your Keycards?
As the security landscape in South Africa continues to evolve, the move toward biometric access control is no longer just a high-tech upgrade—it’s a strategic necessity for any modern organization. By implementing fingerprint access control, you replace the inherent risks of lost, stolen, or shared plastic badges with a system that is as unique as the people it protects. Ultimately, securing your personnel, data, and assets shouldn’t be a gamble on a piece of plastic; it should be as reliable and seamless as a single touch.